13 May Meeting SecurityMetrics PCI Compliancy when using MDaemon
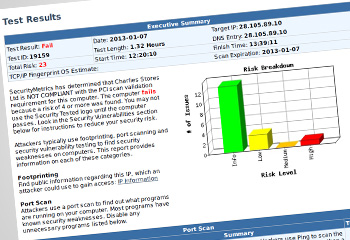 We have recently been dealing with a range of customers who are using the SecurityMetrics PCI compliance check on their network and are in the process of working through the highlighted security vulnerabilities the report has brought to their attention. These vulnerabilities reports highlight any issues with any public-facing services on your network but often include many checks against your email services including MDaemon. With any software, the way it is configured plays an important part in how it meets the security needs and MDaemon is no different in this respect. Before we look at some of the more detailed aspects the first recommendation is always to upgrade MDaemon to the current release before you re-run the PCI compliance tests as security updates are included in each release and do address previous known issues.
We have recently been dealing with a range of customers who are using the SecurityMetrics PCI compliance check on their network and are in the process of working through the highlighted security vulnerabilities the report has brought to their attention. These vulnerabilities reports highlight any issues with any public-facing services on your network but often include many checks against your email services including MDaemon. With any software, the way it is configured plays an important part in how it meets the security needs and MDaemon is no different in this respect. Before we look at some of the more detailed aspects the first recommendation is always to upgrade MDaemon to the current release before you re-run the PCI compliance tests as security updates are included in each release and do address previous known issues.
Once you are happy that your MDaemon installation is up to date the next step is to look in more detail at each highlighted security vulnerability in the PCI report to be able to match this to the relevant feature configuration in MDaemon that relates to it.
So far each PCI report we have worked on has highlighted different specific issues for each customer installation, but there are some common issues that have cropped up that can be easily addressed.
Here are the top 4 most common issues that we have seen:
1. Plain text passwords allowed using insecure protocols
Using unsecured versions of the email protocols is the number one security risk. Unsecured protocols allow a username and password to be sent to the server in a plain text form and so this is easily captured on a network and can be used to further compromise the server.
Our recommendation is to only allow plain SMTP access publicly and restrict POP3 and IMAP access to the secured SSL versions both publicly and even internally on your network.
As well as turning on the SSL version so of the protocols within MDaemon it is advisable to firewall access at the port level so it is impossible to connect externally to the default ports (110 and 143).
Fix: Configure SSL versions of IMAP, POP3 and WorldClient
Fix: Un-select the ‘Allow plain text passwords’ option to force connections to use Encrypted passwords
2. Weak SSL Ciphers
Using SSL certificates is still open to more advanced attacks if the strength of the encryption method in the operating system itself is not high enough. By restricting the weaker encryption methods in the operating system MDaemon is protected against these types of attacks.
Fix: Restrict the use of Weak SSL Ciphers in Windows by following this guide
3. Using a self-signed SSL certificate
The simple and most cost-effective way to set up SSL is to use a self-signed certificate. By design these are not inherently trusted globally and can be set up by anyone so does not guarantee the authenticity of the server.
The more secure approach is to purchase a root trusted SSL certificate from a root trusted certificate provider. These are trusted by the clients natively and checks are performed on the domain holder by the SSL certificate provider before the SSL certificate is issued.
Fix: Purchasing a self Signed SSL Certificate
4. SMTP relaying open to attack
A classic way to compromise any email platform is to use it to relay spam mail on your behalf. By sending one email from either an internal or external email address with a destination of many different external addresses a spammer can get your mail server to do all their work and hide the original sender. Mail Relaying can be restricted within MDaemon’s relaying options. When a spammer tries to relay a message claiming to be from an internal email address this is known as spoofing and can be restricted within MDaemon IP Shielding settings.
Fix: Restrict relaying and require valid MAIL FROM / RCPT TO
Fix: Protecting your server from spoofing using MDaemon’s ‘IP Shielding’ feature
If you do run a PCI vulnerability test and come across any other issues please feel free to contact us in Support and let us help you find what changes can be made to resolve them.
Related articles
- MDaemon: How to pre-check email before it’s sent (Editor approval) (zensoftware.co.uk)
- New video: Introduction to MDaemon webinar recording (zensoftware.co.uk)

