11 Dec Let’s Encrypt, Free SSL Certificates for MDaemon Email Server –
Cybercrime. Isn’t it just the gift that the keeps on giving?
Picture the scene…
You’re about to catch a flight, the final boarding call is but minutes away and you remember an email you absolutely had to get sent before take off.
Plucking your laptop from the post luggage check cable spaghetti, you perch in the lounge, successfully connect to the free wifi and hammer out your email masterpiece.
As you don the noise cancelling headphones and breathe a sigh of relief, you’re blissfully unaware that the chap in the lounge you’d assumed was buried in a spreadsheet, was actually running the data ‘sniffing’ software Wireshark.
Not many minutes later, you’re at 30,000 feet and he’s walking away with everything he needs to send email as you, and to view the sensitive contents of your messages (take a look at this video to see just how easy it is!) and to cause havoc for your business.
Not a nice hypothetical.
So what can you do to prevent it happening for real?
As business email users, we know we should be using a decent spam and virus filter, and we have a pretty good idea of what to look for in terms of messages that are likely to cause us problems. However, we are still sometimes complacent when it comes to what happens after we hit ‘send’.
As a minimum, what we should all be doing without exception, is encrypting our email communications using SSL (a Secured Socket Layer).
What is an SSL?
Whenever you connect to your mailbox, whether it’s using IMAP or POP, without an SSL, that username and password are sent across the Internet in cleartext.
This means that if you’re using an unsecured wireless connection or sharing your network with others, anyone else on that network has the opportunity to sniff your packets (if you’ll excuse the expression).
An SSL connection encrypts your email traffic so it can’t be read at any point between your computer and the MDaemon mail server that you’re using.
Introducing Let’s Encrypt
Historically, to secure your communications in MDaemon using SSL you’d either have to use the self-signed certificate option, which isn’t natively trusted and is less than simple to implement, or a paid root trusted certificate which works great, but has a cost associated.
Let’s Encrypt is a Certificate Authority (CA) that provides free certificates and is quite simply the best of both worlds.
Not only are the certificates free of charge but with the support for Let’s Encrypt in MDaemon, the otherwise complex process of manual creation, validation, signing, installation, and renewal, is all automated and completely hassle-free.
MDaemon help guide: Creating and using SSL certificates
Using a Let’s Encrypt certificate with MDaemon
Thankfully, the MDaemon developers have taken the hard work out of registering and renewing the certificate and there are only a few simple steps needed to set one up and let it self-manage the renewals every few months.
Prerequisites
Powershell
Before we get started, it’s worth noting that Let’s Encrypt scripts require PowerShell V5.1 or above, so will not work on Server 2003 O/S variants. Also required is Net Framework 4.7.2 or above.
Newer versions of Windows server will have the required version of PowerShell installed already.
Ports and webmail binding
In order for the Let’s Encrypt registration process to validate your hostname and installation, MDaemon’s webmail web server must have port 80 traffic open to the Internet.
This means you’ll need to make sure you add the following line under the webmail bind options.
*,*:80
(this tells webmail to also respond to web traffic on port 80 on any network interface)
Enabling Let’s Encrypt
The domain that will be used by the Let’s Encrypt certificate will be the SMTP host name as defined on the primary domain under Settings > Domain Manager.
If you need the certificate to be valid for additional hostnames, you can add these as alternative hosts on the next step.
Navigate to Security Settings -> SSL & TLS -> Let’s Encrypt and enable the updates.
Next enter an email address to receive any error reports.
I recommend leaving the renewal time at 60 days to allow the renewal to retry should there be any issues.
Choose OK to save the options and trigger the script to register your certificate in the background.
Click RUN Now then OK to save the settings and if all goes well the MDaemon interface should restart shortly afterwards and a new Let’s Encrypt certificate should have been installed.
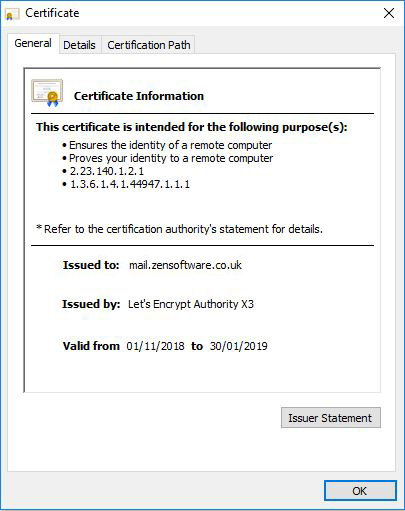
You can test if this certificate is bounded correctly by pointing a web browser to the Webmail service and view the certificate properties.
Finishing off
Make sure the new Let’s Encrypt certificate is selected for the services you’d like to be using it.
You can check this under Security -> Security Settings -> SSL &TLS -> MDaemon and Security -> Security Settings -> SSL &TLS -> MDaemon -> Webmail.
If you have any old self-signed certificates here, this is a good time to remove them to avoid confusion.
Last but not least, redirect the standard HTTP Web traffic on port 80 to the HTTPS port 443.
This will still allow Let’s Encrypt updates to work. They will still connect on port 80 but will work via a redirect (it’s not good practice to leave port 80 open publicly).
To do this navigate to Setup -> Webmail -> SSL & HTTPS and choose the option HTTP redirected to HTTPS from the list of accepted connection types.
There you have it, all the benefits of a root trusted certificate but at no additional cost.
To conclude
We highly recommend SSL, it’s quite simply a no-brainer, significantly improving security for little effort.
It’s important to be aware however that it’s not a silver bullet for security. The bad men shalt still potentially violate your conversations.
In theory, they can still intercept traffic leaving your server, as that’s still in cleartext. For the next level of security, you’ll need to think about using one of MDaemon’s point to point encryption options, linked below.
https://www.altn.com/email-encryption/


