13 Oct Name and Shame – How to Identify Users with Weak Passwords in MDaemon
 Weak passwords are the most common method by which email accounts and servers can become compromised by spammers.
Weak passwords are the most common method by which email accounts and servers can become compromised by spammers.
The great news is that Exchange alternative MDaemon Messaging Server, now offers an easy way to identify when somebody’s using one that isn’t secure via a simple but effective new reporting feature.
Whether you then decide to name and shame, or just to give them a friendly nudge is entirely up to your discretion! :).
Straight out of the box you can now run some basic tests for password strength and will notify you of accounts that need attention, but with a little more work we can also improve on this further.
The ‘weak password’ report feature
So in order to run a report that highlights weak passwords you must first enable ‘Require strong passwords’ under ‘Account -> Account settings -> Other -> Passwords’
Once you’ve enabled strong passwords, you can simply run the report by selecting the button to ‘Report weak passwords‘.
Clicking that will then ask you for an appropriate email address to send the report to detailing any offending accounts.
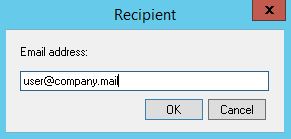
Note – The email won’t actually reveal the passwords of any accounts, just the email addresses.
This basic check is to look for the length and complexity of passwords – this, in most cases, will highlight offenders, but for added protection you can also specify a list of bad passwords to check against.
Bad password lists
For the best security, single word passwords shouldn’t really be used, so if you’re looking for the highest quality passwords you want to consider adding very large word dictionaries to the bad lists.
If you need a bad password list I’d recommend just Googling for ‘word lists’ or ‘common passwords’.
Passwords to look out for include:
- Any of the usernames on the MDaemon server (an easy guess for any attacker)
- List of names people and places
http://www.outpost9.com/files/WordLists.html - Frequently used passwords
http://www.whatsmypass.com/the-top-500-worst-passwords-of-all-time
http://weakpass.com/lists
…but there are many others, just Google for ‘Word lists’ or ‘Common Passwords’
To build a word list simple create a text file with a single word per line and click to edit the bad password file.
You can make this as large as you like but bear in mind this will mean the report will take longer to run.
I hope that helps you boost your server security – if you’ve got any questions please feel free to let me know in the comments!

